1 – Premises
The EU has begun to deal concretely with information security since 2004 when the ENISA (European Union Agency for Cybersecurity) was established and in whose first advisory committee the writer took part.
A 2009 Commission Communication defined a first plan for the promotion and strengthening of the security of the digital society. Issued in 2013 is a joint communication of the Commission and the High Representative of the Union for Foreign Affairs and the Security Policy of the Union for Foreign Affairs and Security Policy concerning a common strategy for the cybersecurity of the member countries.
However, it is only in recent years that two truly binding milestones from a regulatory point of view have been laid: Regulation (EU) 2016/679 (General Data Protection Regulation) and Directive (EU) 2016/1148 better known as the NIS Directive. We do not want to deal with a detailed examination of the two rules here. Rather, we want to observe how the two provisions concern aspects of the protection of the digitized society that are profoundly different from each other, shedding light on some inconsistent contaminations, at least in the opinion of the writer, often found during the practical implementation of the above-mentioned provisions in companies and industries.
Having clarified this aspect, we will then move on to talk about the implementation aspects of the NIS regulation and to propose, in this regard, an operational support recently made available.
In today’s digitized society we can distinguish two major application domains of digital technologies: the first that conventionally in this article we name administrative and the second we name techno-industrial. The first, now more than mature and adequately regulated both in terms of standards and legislation, concerns the processing of information (i.e. data, when they are processed by computers) of administrative and business management nature. It is the domain of general accounting, payroll accounting, commercial orders, contracts, e-mail, medical records, e-commerce and so on. Most of these data have, directly or indirectly, to do with persons and, consequently, with their rights. In this domain it is generally agreed that data protection should refer to three parameters: confidentiality, integrity, and availability. Such triad is primarily taken into account, when preparing a protection plan in the important and recommended risk analysis phase.
In this regard, a few decades ago the writer coined the term CIA (Confidentiality-Integrity-Availability) triad. It should be noted that, in this context, the data entry is performed by a person or by some behavior of he or she, often with the mediation of technical equipment and some type of automatism. The result of the processing in most cases is intended, directly or through an event that concerns him, to a person (natural or legal): the crediting of a salary in the bank, the sending of an e-mail, the delivery of a purchased item, updating a medical record and so on. Such data are specifically referenced by the GDPR.
On the other hand, more recently, the enterprises have become aware of the need to protect digital platforms of another type: those that belong, in fact, to the techno-industrial domain. This area includes various scenarios: automotive, building automation, industry 4.0 and beyond, smart cities, production and distribution of energy and services and much more. In this type of platform, the data entry for processing is carried out by sensors, the processing is carried out by multiple small computing units often equipped with sui generis operating systems. The data travels thanks to proprietary protocols and the results are for the benefit, rather than for human beings, for actuators that regulate the most disparate technical functions. Consequently to the above, being most of the data processed by this type of platform not related to persons, but above all having, in terms of
protection, to guarantee the functional continuity of the platform itself , some reflections appear justified which we will carry out below. Before doing so we report hereunder a table that summarizes significantly, although probably not exhaustively, the difference between the two worlds.
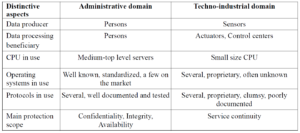
Most of the companies that requires compliance with the NIS legislation (Operators of Essential Services and Digital Service Provider) find themselves having to consider techno-industrial IT platforms as an object to be protected. In other words, the goal is to ensure the continuity of the service rather than the confidentiality, integrity and availability of information.
2 Peculiarities of techno-industrial platforms
The administrative platforms (in the sense indicated above) are made up of a set of servers, fixed and mobile clients, auxiliary storage devices and more placed locally, on the move or in the cloud. This set of resources treats the information that travels through connections physically made with various transmission technologies, using well-known and fully defined protocols.
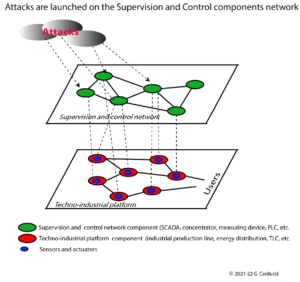
For their part, the techno-industrial platforms, which we are now dealing with, are characterized by a double level, as indicated in the figure on the following page.
A level (indicated in the figure as a techno-industrial platform) is the set of components that, functionally connected to each other, create the service or production cycle that is the company’s raison d’être. For example, in the energy distribution sector, it is the set of electrotechnical equipment (components) located in primary and secondary substations as well as the physical conductors that conduct the energy to the measuring devices and for use by the end user.
The range of these components includes various types of sensors and actuators that allow connection to the second level platform.
This second level platform (in the followingfigure indicated, in reality, above the previous one and called the Supervision and Control Network) is made up of a set of interconnected components (concentrators of communication lines, Remote Terminal Units and more), equipped with computational and logical capacity of variable power.
On the one hand, these components refer to a centralized software application (normally of the SCADA type) located in the manned control Operational Center; on the other hand, through various communication lines, they are connected to sensors and actuators. The latter, which are an integral part of the techno-industrial platform, send and receive signals that allow, through the SCADA
application, to manage the functionality of the industrial process. The communication channels among the various components of the two platforms, are physically characterized by various types of technologies and often use proprietary and insufficiently documented protocols.
3 – Specificity of risk analysis in techno-industrial platforms
All the above allows to support the following statement: techno-industrial platforms have their exposure to risk (read: to possible attacks) concentrated in the level of supervision and control. Of course an attacker can destroy a primary cabin or a production facility with an adequate charge of explosive (a physical security issue). However, if we focus on the cybersecurity aspects and imagine that the interruption or disruption of the service is the purpose of the attack by a black hat hacker who wants to operate digitally, the risk analysis must focus on attack points of the various components of the supervision and control network. Consequently, the risk analysis will have to focus on the identification of the vulnerabilities that characterize these components, including the transmission channels and their protocols.
Given as above, the writer has proposed a risk analysis and management methodology (IPSEM – Industrial Platforms Security Evaluation Methodology) which, as now, has been tested in the field in a couple of significant cases. The methodology, in summary, is based on the following steps:
1 – Identification with graphic and textual representation of the components of the Supervision and Control platform.
2 – Identification of known vulnerabilities in the literature or detected by laboratory analysis of the most critical functional components. In this regard, a database of known vulnerabilities (Vargo-el) is currently available for the components of the platforms in the energy distribution sector.
3 – Association of the vulnerabilities found to the individual components (by type). It should be remembered that the components include the transmission channels and the persons assigned to the operations.
4 – Attribution of a criticality index to each type of component using a questionnaire that considers the vulnerabilities detected, the functional criticality that the component has for the functionality of the process and the extent of the damage caused to users if the attack were to succeed. This questionnaire can be customized according to the specific nature of the company and the sector in which the company operates.